|
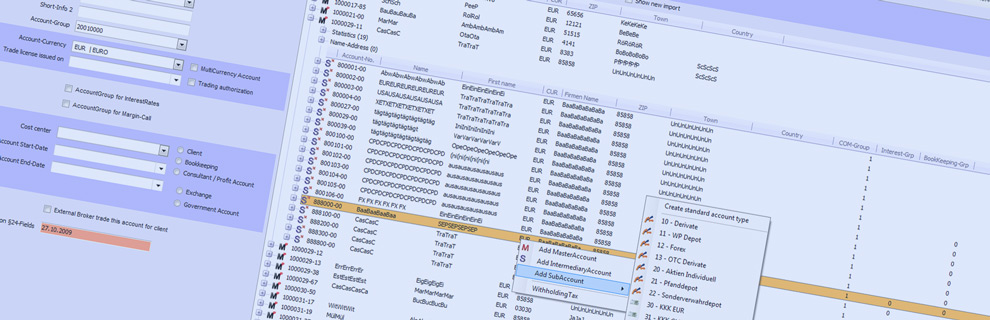
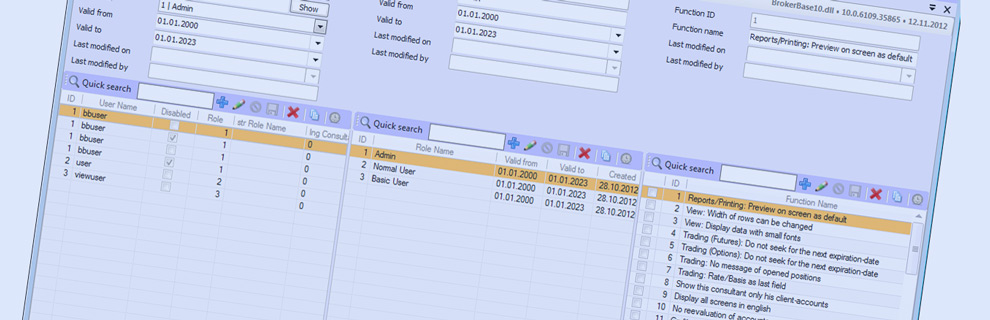
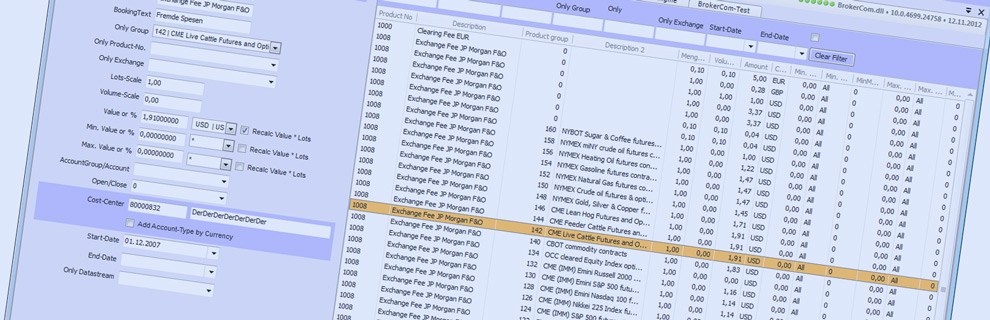
Starting with the version 10.0, BrokerBase provides a first class role-based user management. It allows
role profile creating, which can be limited in time or space (for example in the case of subsidiaries and depending on the IP) .
Adittionally, the application provides you with the possibility to create an unlimited number of users, which afterwards can be assigned to a role. It is also
possible to define a start and end date, that will describe the period in which the user permissions are granted on the BrokerBase. For each mask there is a
minimum of 3 access rules: read, modify and delete, but most of them have more definied permissions.
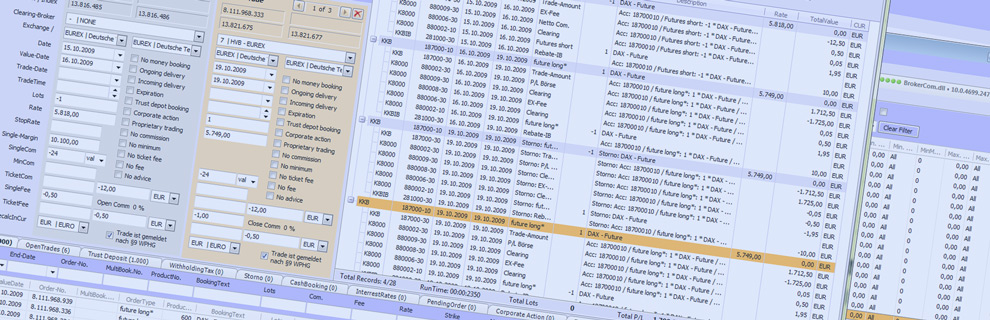
In addition to that, there are access rules that control the technical process, such as the four-eyes principle. In this case, users are divided into groups.
The four-eye principle consists in, for example, crediting system or limits-exceeding.
|
|
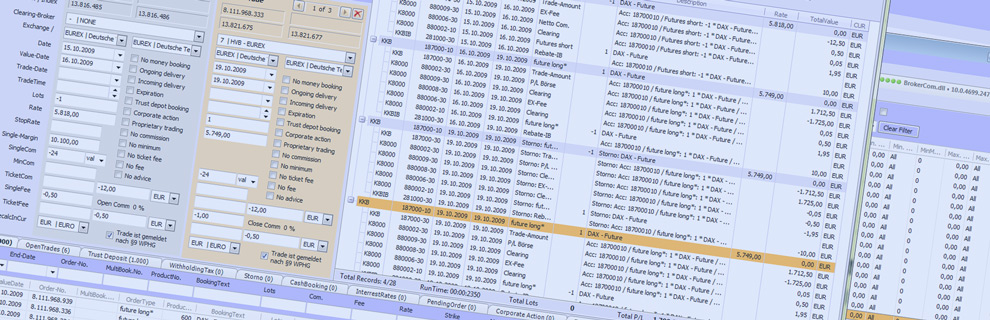
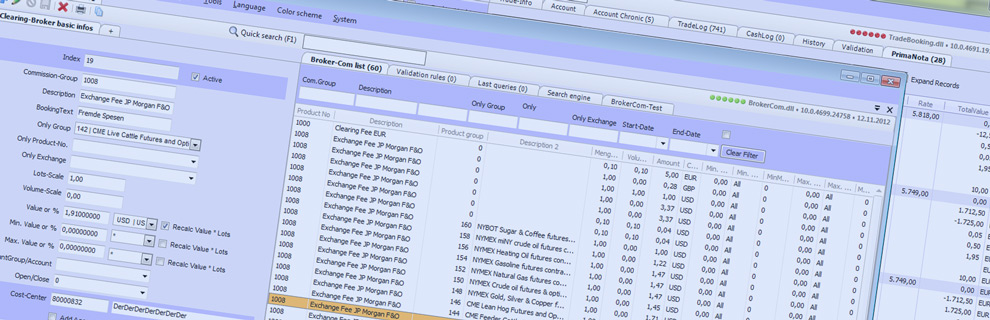
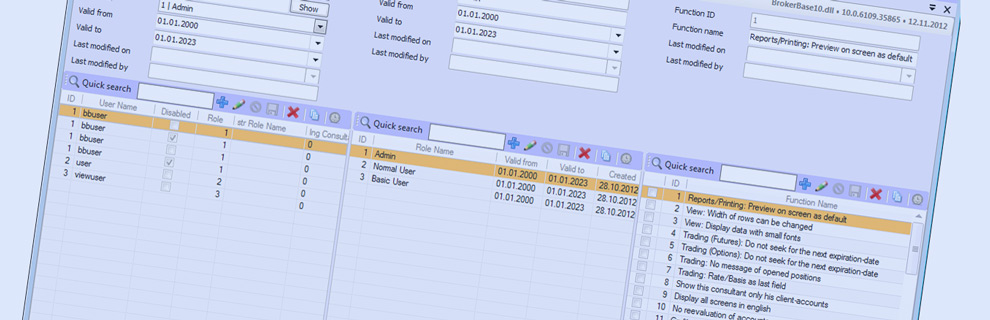
The complete role management is located on the central server and is accessed in subisidiaries using a database synchronising system or a database mirroring.
Once set up, no more tasks are required, all databases, master or slave, are self-sufficient with their own roles or in sync with the master database, just as desired.
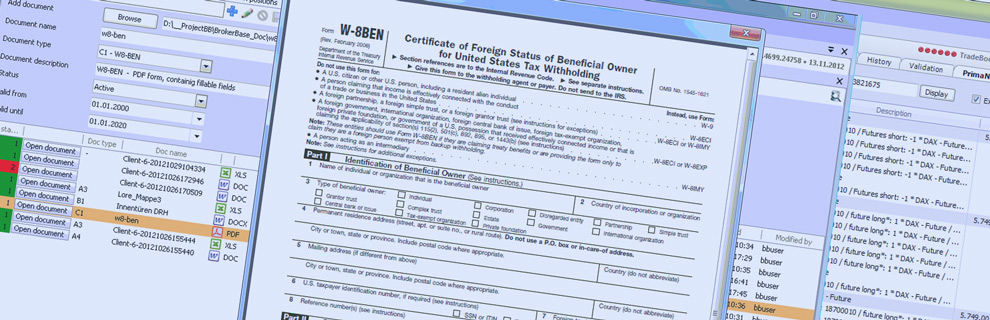
In the background, all user data such as login / logout are logged in the database. Additionally, the user is logged for each record changed or newly created. All these
informations will then be centrally available for the administrator(s) in case of a technical revision.
|
|
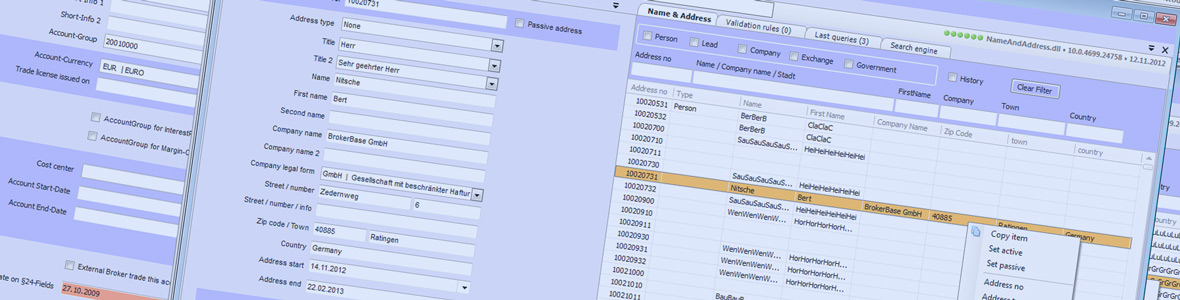
Starting with version 10.0, BrokerBase provides a task assignment function, for example: personal information that has an expiration date, like the identity card,
are constantly maintained by the "back office" user role, and only for this role are the account events displayed.
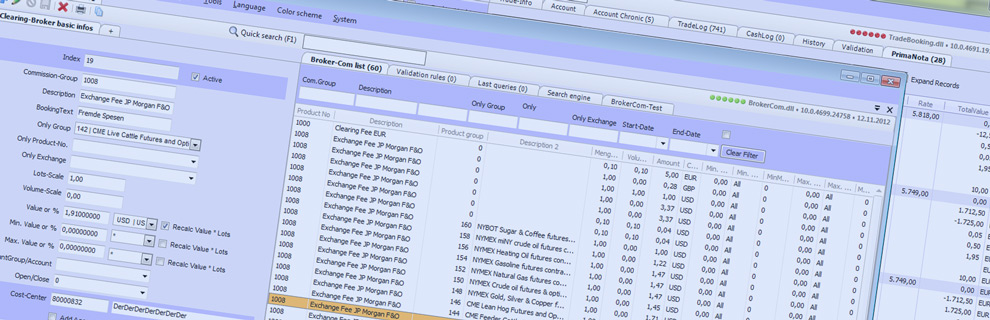
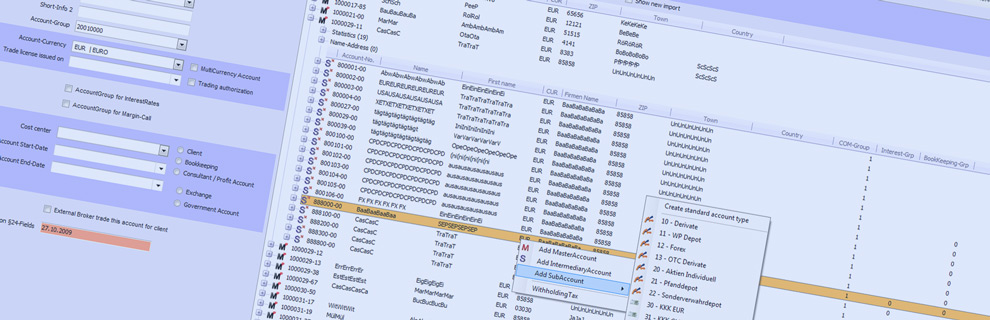
The complete role management is displayed in one mask: all the users, all the roles and their associated functions as well. That is an efficient and simple
managing system that prevents any possible incorrect entries. In addition, each mask will visually display the access rights that are granted or not for the
currently logged in user. This simplifies the administrator's tasks of creating, managing and also debuging the user profiles and roles.
|